Domino can synchronize Domino administrative user roles and organization membership with attributes in your SAML identity provider. Use this to externalize management of these roles and memberships to the identity provider.
The SAML provider application connected to Domino must include group membership as a multi-valued attribute.
To enable this feature, you must update the Domino Central Configuration setting authentication.oidc.externalOrgsEnabled to true, then restart Domino services.
Attribute mapper
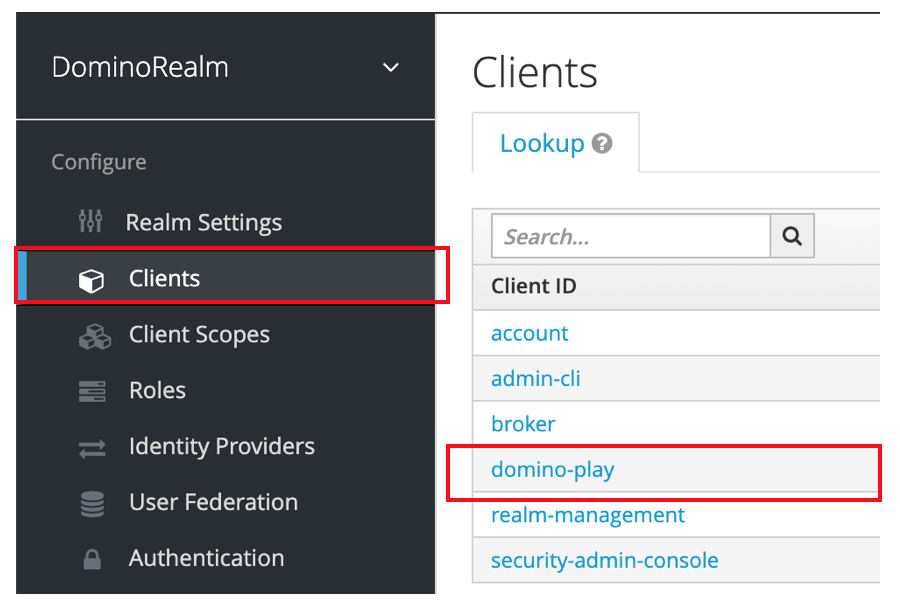
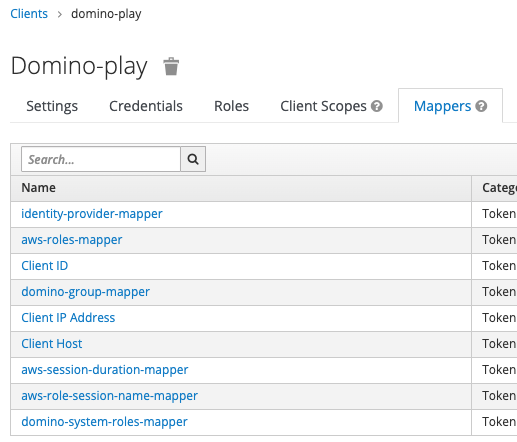
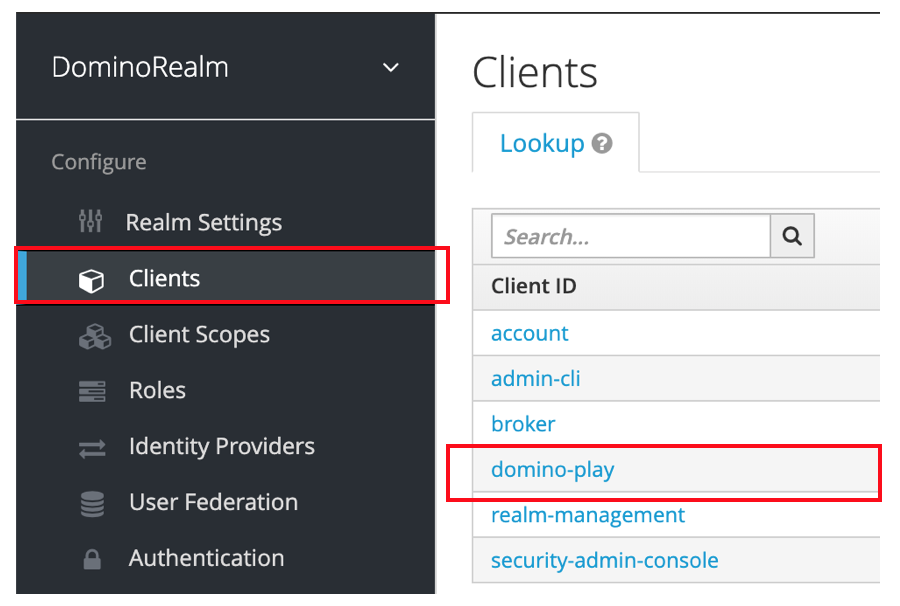
Add an Attribute Importer mapper to the provider configuration in Keycloak.
-
Name: Domino Groups
-
Mapper Type:
Attribute Importer -
Attribute Name: Name attribute for the element that contains the groups for the user.
-
Friendly Name:
FriendlyNameattribute for the element that contains the groups for the user. -
User Attribute Name:
domino-groups.
Example:
<saml2:Attribute Name="UserGroups">
<saml2:AttributeValue>nyc-data-scientists</saml2:AttributeValue>
<saml2:AttributeValue>all-data-scientists</saml2:AttributeValue>
<saml2:AttributeValue>sensitive-claims-users</saml2:AttributeValue>
</saml2:Attribute>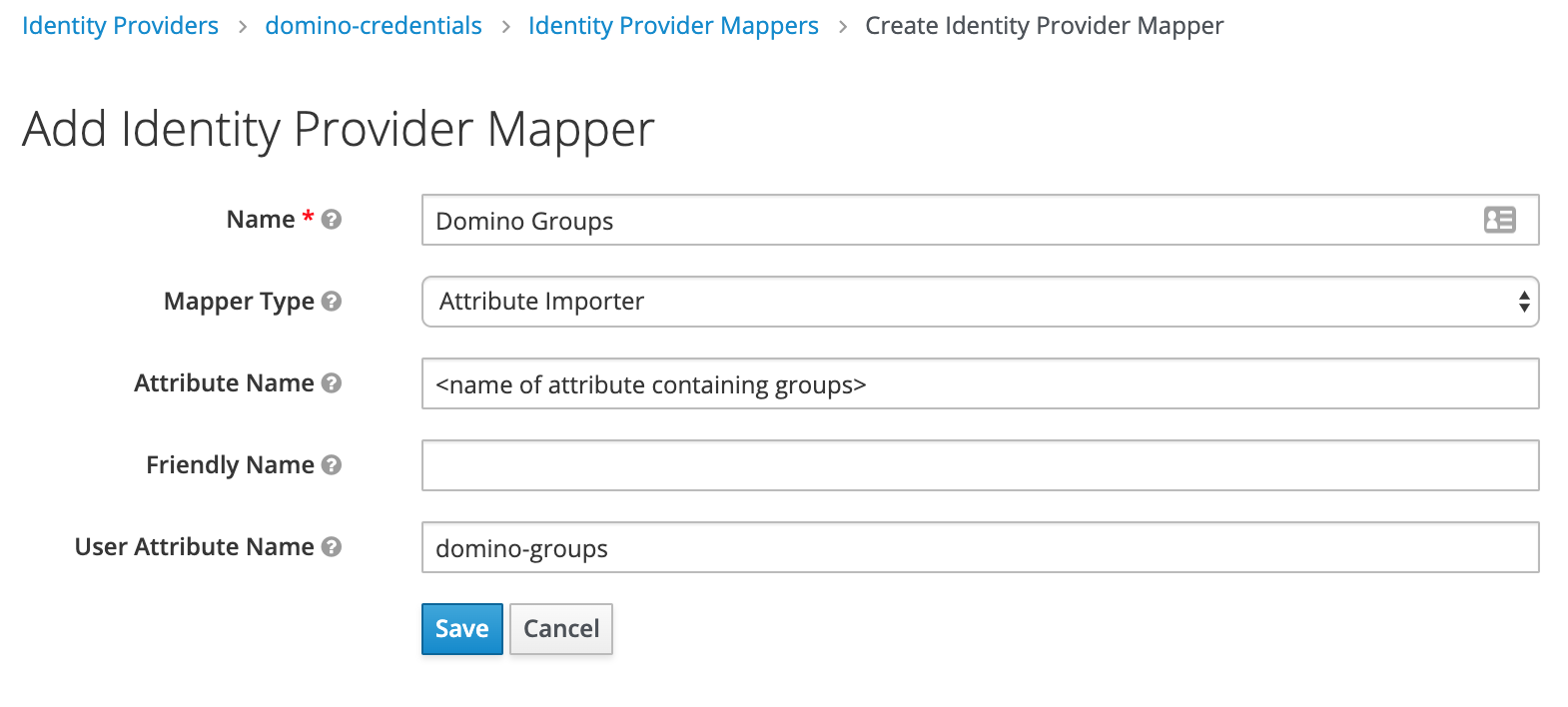
In addition to group membership, you can also automatically assign Domino administrative and/or user roles to users based on attributes from your SAML identity provider.
Attribute mapper
You must add an Attribute Importer mapper to the provider configuration in Keycloak.
-
Name: Domino System Roles
-
Mapper Type:
Attribute Importer -
Attribute Name: Name attribute for the element that contains the Domino system roles for the user.
-
Friendly Name:
FriendlyNameattribute for the element that contains the groups for the user. -
User Attribute Name:
domino-system-roles.
You must include the following attributes if you synchronize groups in Domino.
-
Domino Organizations
-
Name: Can be any name since Domino can map attributes.
-
Multi-valued: Yes
-
Values:
-
One or more of the groups the user belongs to in your centralized identity provider. For any groups specified here, the user will be automatically enrolled in a Domino organization with the same name.
-
-
Example:
<saml2:AttributeStatement xmlns:saml2="urn:oasis:names:tc:SAML:2.0:assertion">
<saml2:Attribute Name="DominoOrganizations">
<saml2:AttributeValue>nyc-data-scientists</saml2:AttributeValue>
<saml2:AttributeValue>all-data-scientists</saml2:AttributeValue>
<saml2:AttributeValue>sensitive-claims-users</saml2:AttributeValue>
</saml2:Attribute>
</saml2:AttributeStatement>Learn how to propagate AWS credentials.