Personal Access Tokens (PATs) are user-managed credentials that allow Domino users to authenticate against the Domino API. Users create their own tokens, each with a name, an optional description, and a custom expiration time.
PATs differ from Domino Service Accounts in that they are personal and tied to an individual user’s identity and roles. They are intended for interactive use, personal scripts, and jobs that a user runs on their own behalf, rather than for shared automation pipelines.
As an administrator, you can view and revoke any user’s tokens, perform bulk operations across users, and review token activity across the platform. Administrators cannot generate PATs on behalf of other users — each user must create their own tokens from their account settings or via the API.
|
Important
| Administrators can only access PAT metadata — such as the token name, owner, status, and expiration date. The JWT token value itself is never accessible after creation, even to administrators. This is by design: a PAT can only be retrieved by the user who created it, at the moment of creation. Administrators can revoke or delete a token, but cannot read or use it. |
You can access the PAT administration panel in two ways:
-
Navigate directly to
/admin/personalaccesstokens. -
From the top navigation bar, go to Manage resources > Personal Access Tokens.
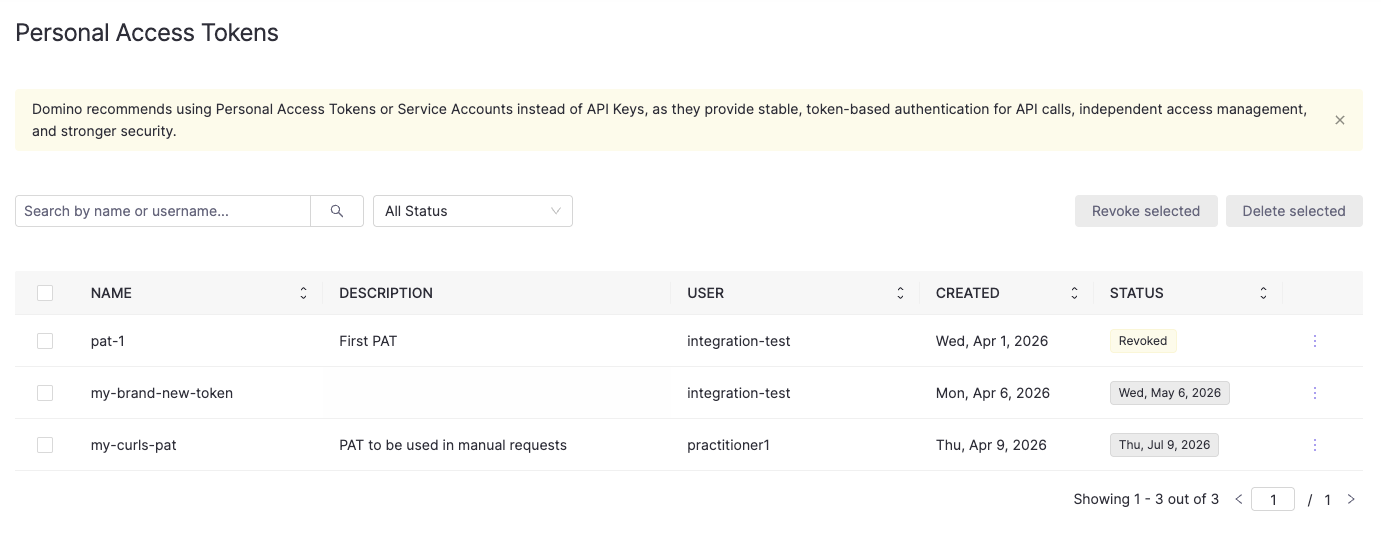
The panel displays all PATs across every user in the platform. Each row shows the token name, description, owner username, creation date, last used date, and current status.
The STATUS column shows either a status badge (Revoked, Expired) or the token’s expiration date for active tokens.
You can narrow down the list using:
-
The Search by name or username field — filters by partial token name or username.
-
The All Status dropdown — filters by
Active,Expiring Soon,Expired, orRevoked.
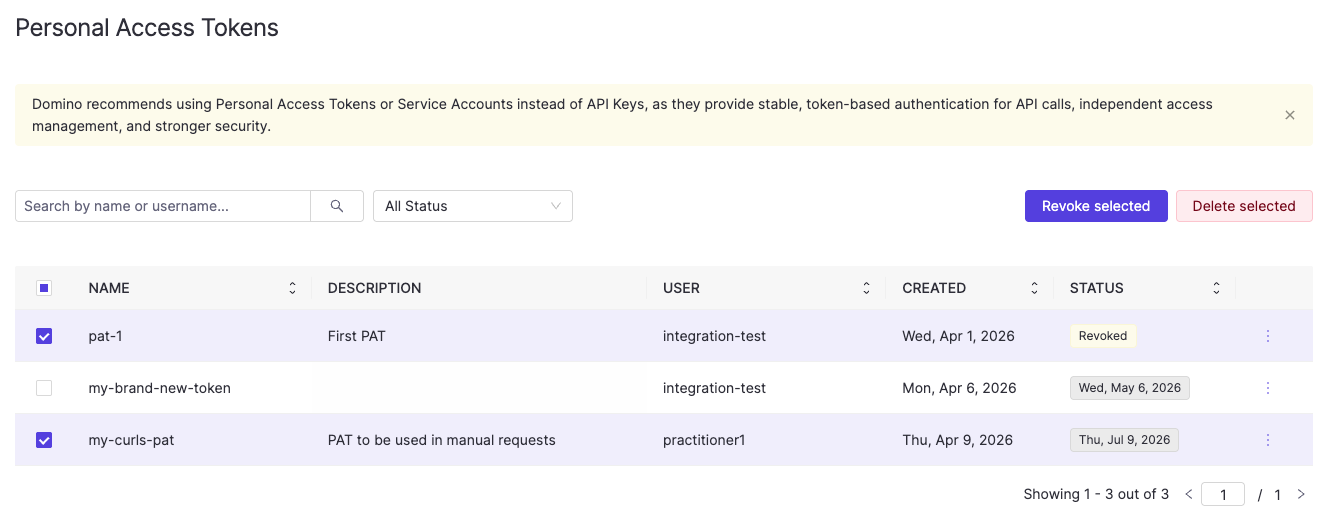
Each row has a checkbox on the left for bulk selection. When one or more tokens are selected, Revoke selected and Delete selected buttons appear in the top right of the table.
The admin panel provides a UI view of all tokens, but you can also retrieve them programmatically.
Example endpoint information:
GET /api/pat/v1/users/tokensExample curl request (calling inside Domino):
curl -H "Authorization: Bearer $DOMINO_ACCESS_TOKEN" \
"$DOMINO_API_PROXY/api/pat/v1/users/tokens"Example response:
{
"tokens": [
{
"patId": "64b1c2d3e4f5a6b7c8d9e0f1",
"userId": "5f3a7b2c1d4e6f8a9b0c1d2e",
"username": "alice",
"name": "my-domino-token",
"description": "My personal Domino API token",
"isValid": true,
"createdAt": "2024-04-01T10:00:00Z",
"expiresAt": "2024-04-08T10:00:00Z"
}
],
"pagination": {
"offset": 0,
"limit": 10,
"total": 1
}
}You can filter and sort results using the following query parameters:
| Parameter | Default | Description |
|---|---|---|
| — | Filter by partial token name or username match. |
| — | Filter by token status: |
|
| Sort by: |
|
| Sort direction: |
|
| Pagination offset. |
|
| Number of results per page. |
View tokens for a specific user
Example endpoint information:
GET /api/pat/v1/users/{userId}/tokensExample curl request (calling inside Domino):
curl -H "Authorization: Bearer $DOMINO_ACCESS_TOKEN" \
"$DOMINO_API_PROXY/api/pat/v1/users/$USER_ID/tokens"Supports the same query parameters as the system-wide listing above.
Some administrative actions on a user account automatically affect their PATs:
-
When a user is deactivated, all their PATs are automatically deleted.
-
When a user’s roles are modified, all their PATs are automatically revoked. The user will need to create new tokens to authenticate with their updated permissions.
In both cases, no manual action is required from the administrator. The sections below cover situations where you need to revoke or delete tokens independently of these lifecycle events.
Revoking a token immediately invalidates it while keeping its metadata visible. Both the user and administrators will still see the token listed with a revoked status, so they are aware it was invalidated and can choose to delete it later.
Revoke a single token
In the PAT admin panel, click the three-dot menu at the end of the token row and select Revoke.
Alternatively, use the API:
Example endpoint information:
POST /api/pat/v1/users/{userId}/tokens/{patId}/invalidateExample curl request (calling inside Domino):
curl -X POST \
-H "Authorization: Bearer $DOMINO_ACCESS_TOKEN" \
$DOMINO_API_PROXY/api/pat/v1/users/$USER_ID/tokens/$PAT_ID/invalidateRevoke all tokens for a user
Use this when you need to immediately invalidate all of a user’s tokens, for example when responding to a suspected credential compromise.
Example endpoint information:
POST /api/pat/v1/users/{userId}/tokens/invalidateExample curl request (calling inside Domino):
curl -X POST \
-H "Authorization: Bearer $DOMINO_ACCESS_TOKEN" \
$DOMINO_API_PROXY/api/pat/v1/users/$USER_ID/tokens/invalidateRevoke multiple tokens in bulk
In the PAT admin panel, select the checkboxes next to the tokens you want to revoke and click Revoke selected.
Alternatively, use the API:
Example endpoint information:
POST /api/pat/v1/users/tokens/invalidate/bulk
{
"patIds": ["64b1c2d3e4f5a6b7c8d9e0f1", "74c2d3e4f5a6b7c8d9e0f1a2"]
}Example curl request (calling inside Domino):
curl -X POST \
-H "Authorization: Bearer $DOMINO_ACCESS_TOKEN" \
-H "Content-Type: application/json" \
-d '{"patIds": ["64b1c2d3e4f5a6b7c8d9e0f1", "74c2d3e4f5a6b7c8d9e0f1a2"]}' \
$DOMINO_API_PROXY/api/pat/v1/users/tokens/invalidate/bulkDeleting a token permanently removes it and all its metadata. Once deleted, neither the user nor administrators will be able to see it. Rather revoke the token if you want the token to remain visible after it has been invalidated.
Delete a single token
In the PAT admin panel, click the three-dot menu at the end of the token row and select Delete.
Alternatively, use the API:
Example endpoint information:
DELETE /api/pat/v1/users/{userId}/tokens/{patId}Example curl request (calling inside Domino):
curl -X DELETE \
-H "Authorization: Bearer $DOMINO_ACCESS_TOKEN" \
$DOMINO_API_PROXY/api/pat/v1/users/$USER_ID/tokens/$PAT_IDDelete multiple tokens in bulk
In the PAT admin panel, select the checkboxes next to the tokens you want to delete and click Delete selected.
Alternatively, use the API:
Example endpoint information:
POST /api/pat/v1/users/tokens/delete/bulk
{
"patIds": ["64b1c2d3e4f5a6b7c8d9e0f1", "74c2d3e4f5a6b7c8d9e0f1a2"]
}Example curl request (calling inside Domino):
curl -X POST \
-H "Authorization: Bearer $DOMINO_ACCESS_TOKEN" \
-H "Content-Type: application/json" \
-d '{"patIds": ["64b1c2d3e4f5a6b7c8d9e0f1", "74c2d3e4f5a6b7c8d9e0f1a2"]}' \
$DOMINO_API_PROXY/api/pat/v1/users/tokens/delete/bulk-
See Domino API authentication for how users create and manage their own PATs.
-
Explore the Domino REST API reference for additional API details.
